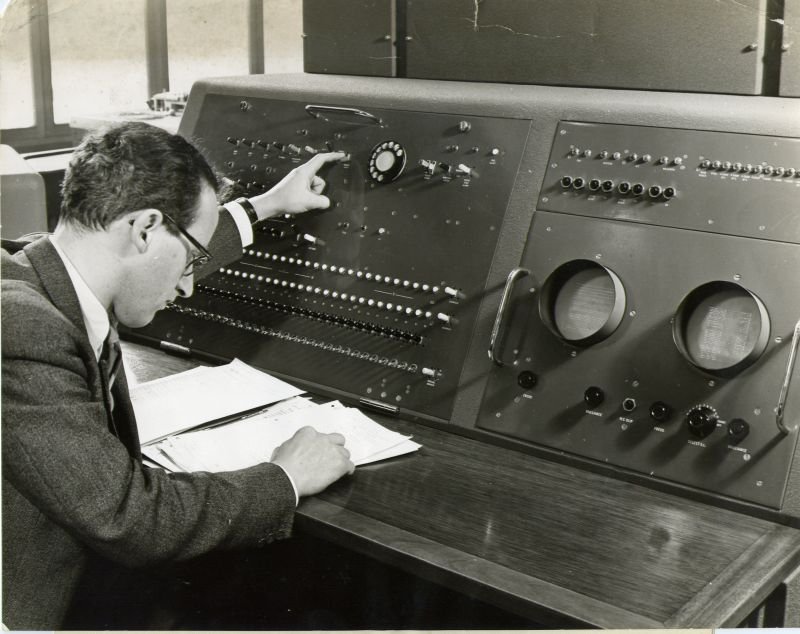
George Davis and Deuce
| Resurrection Home | Previous issue | Next issue | View Original Cover | PDF Version |
Computer
RESURRECTION
The Bulletin of the Computer Conservation Society
ISSN 0958-7403
Number 47 |
Summer 2009 |
| Chairman’s Report | David Hartley |
| Arthur Rowles and the Elliott 401 | Doron Swade |
| Editor’s Remarks | Dik Leatherdale |
| News Round-Up | |
| Society Activity | |
| Pioneer Profiles - Seymour Cray | Dik Leatherdale |
| The Seizing of Singer | Michael Knight |
| Virtual Objects and the End of the Real | Doron Swade |
| Obituary: Peter Hall | Reay Atkinson |
| Forthcoming Events | |
| Committee of the Society | |
| Aims and Objectives |
| Top | Previous | Next |
The BCS is in the process of a substantial reorganisation and the full implications for the CCS are as yet unknown. The BCS is adopting a new financial year and Specialist Groups are being asked to change the dates of their AGMs to a time in September or October. The CCS Constitution was last amended in 1999 and it would be appropriate to conduct another review to bring it into line with current practices.
The Committee has agreed two actions - firstly, to set up a small working group to review the Constitution and to make proposals, and then to put a revised Constitution before an Extraordinary General Meeting on 15 October 2009.
 |
|
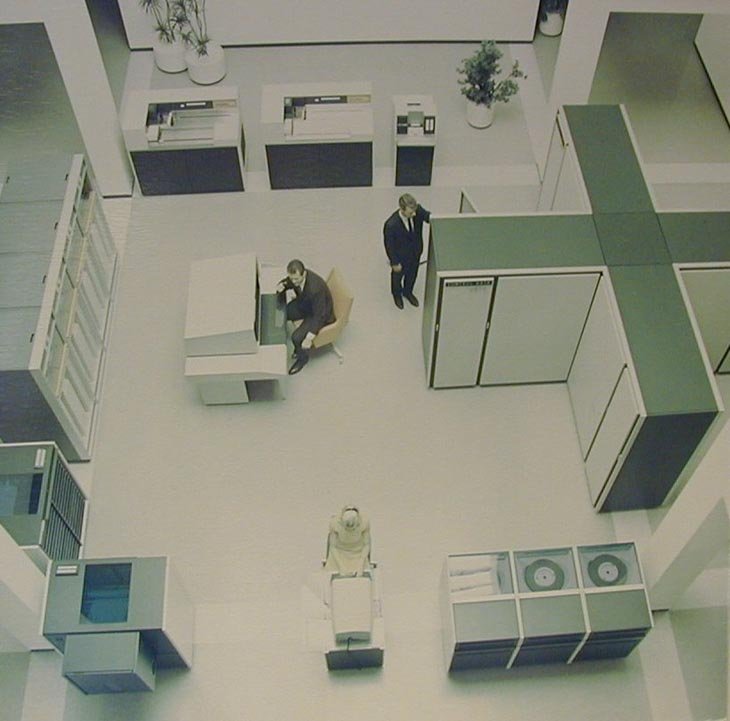
George Davis and Deuce |
Both Peter Barnes and George Davis have indicated their wish to retire from the CCS Committee. Peter has served from 2003, whereas George has been on the Committee since the CCS was founded in 1989. We thank them both for their support, but most especially George who for eight of his 20 years on the Committee was also Meetings Secretary.
After five fruitful years, Arthur Rowles has decided to step down as chairman of the Elliott 401 Working Party. Doron Swade pays due tribute to his work below. I can do no more than echo his fine words.
In view of the need for a constitutional review, the Committee is recommending that, as a temporary measure, all other current officers and committee members are re-elected en bloc.
 |
|
Nicholas Enticknap receives a token of appreciation from BCS Vice-president Adrian Walmsley |
At last year’s AGM, I announced that Nicholas Enticknap who had edited Resurrection from its first issue in 1990 had decided to step down after 42 issues. As I wrote in his last issue, the CCS Committee owes him a great debt for so much skilled, professional, and selfless support given for so long. 42 issues, all to the same standard, is no mean achievement.
I also announced that Dik Leatherdale, a member of the Society, had come forward and has now been editing Resurrection for the past year. Dik has proved to be both enthusiastic and conscientious, and Resurrection has continued to appear with the same quality as before, already with some innovations. Similarly, Alan Thomson has continued for a second year as website editor, providing quality and timely information on CCS news and events.
Our Meetings Secretary, Roger Johnson, produced another interesting and varied programme. At the start of the season, with the LEO Society, we were able to host a tribute to the late David Caminer, while at the end there was a meeting covering the BBC Domesday project. In between, lectures ranged from love letters generated on the Manchester Mark I, to the JANET network now 25 years old, reviews of early EMI computers and the ICL-Fujitsu technology collaboration. We took advantage of a visit to the UK of Charles Bachman, the database pioneer, when he spoke about his life with databases.
The North West branch also held a varied series of events, including repeats of the successful BBC Micro seminar and one on the applications of CAFS, both held in London the year before. An unusual departure was a visit to Jodrell Bank. We continue to be grateful to our two associated museums in London and Manchester for acting as hosts to CCS meeting programmes.
Technical progress in the various CCS projects is reported regularly in the news sections of Resurrection.
Since its official switch-on in 2007, the Turing Bombe project continues to be hailed as a remarkable achievement, and is attracting many visitors to the cryptography museum at Bletchley Park. A highlight of the year was the receipt of a Heritage Award from the Institution of Mechanical Engineers. The Bombe now proudly wears a large metal plaque designed more for the front of old railway locomotives than for a complex calculating machine.
Alongside the Bombe at Bletchley Park, the rebuilt Colossus continues to be a star attraction in the National Museum of Computing, where many other old systems have been installed and brought to working order.
Following environmental and power supply problems in 2007-08, the Pegasus at the Science Museum is now back in full service as the oldest working computer in the world, while the “Baby” attracts visitors to the Museum of Science and Industry in Manchester. The CCS North West Branch joined with Manchester University in celebrations of the 60th anniversary of the “Baby”, and we awarded BCS anniversary medals to four of the pioneers who built the original machine.
The Committee has recently conducted a review of the Elliott 401 project, and is hopeful that this very important machine can be brought to working order in the not too distant future.
Finally, the Committee extended an invitation to the ICT 1301 project located at Pluckley in Kent to join the CCS as one of our projects. This possibility had been mooted some time previously, and we are delighted that they have agreed to join us. The 1301, affectionately known as Flossie, is housed in a barn on a farm and is in partial working order. We hope that our involvement will help speed the machine to full operational status.
| Top | Previous | Next |

To widespread regret Arthur Rowles is standing down as chairman of the 401 Working Party. Arthur has led the 401 restoration for the past five years, ably assisted by Peter Holland and Peter Lawrence. Under Arthur’s stewardship the Working Party met for two days each fortnight for five years - a record of metronomic consistency. On 23 April, the CCS Committee met on site at the Science Museum’s Blythe House store, Hammersmith, where the 401 resides, to review the project. Encouraged by progress, there was a robust commitment to continue. The 401 is a one-off vacuum-tube machine completed in 1953. It was the third machine restoration undertaken by the CCS and work started in the early 1990s. The early restoration involved a phenomenal piece of digital archaeology. There was no metadata available for the magnetic drum. Tony Sale and Chris Burton devised a system of reading the analogue waveforms from the drum, importing these to a PC, and analysing their content and structure. This was a substantial accomplishment and signalled to others what was achievable in retrieval from undocumented magnetic sources. The project is indebted to Arthur for accepting the chairman’s baton and keeping us in the race.
| Top | Previous | Next |
By the time this edition is drops onto your doormat it will be all but 20 years since the Computer Conservation Society was founded. So, happy birthday to us then! Another year and we can crack open the Beaujolais!
I am delighted to announce the appointment of David Barron as Associate Editor of Resurrection. Readers will have seen two of his beautifully-written contributions in recent editions and the opportunity to involve him more fully was too good to pass up. So David will now bring his undoubted talents to what I suppose we must now think of as the Editorial Board. Welcome aboard David.
And now, another apology for the tardiness of Resurrection 46. No excuses. Just a mix up. Sorry.
The profile in this edition moves outside the UK for the first time. Seymour Cray is too important to be ignored. Resurrection, of course, is a publication which is interested in the history of computing from a British perspective. But it seems to me that, to get a rounded view, we need to consider events, people and machines beyond our own shores. Not least in America where so much was and is still achieved. Although the British contribution to computers is often underrated in the US, it would not do, I submit, to make the opposite mistake.
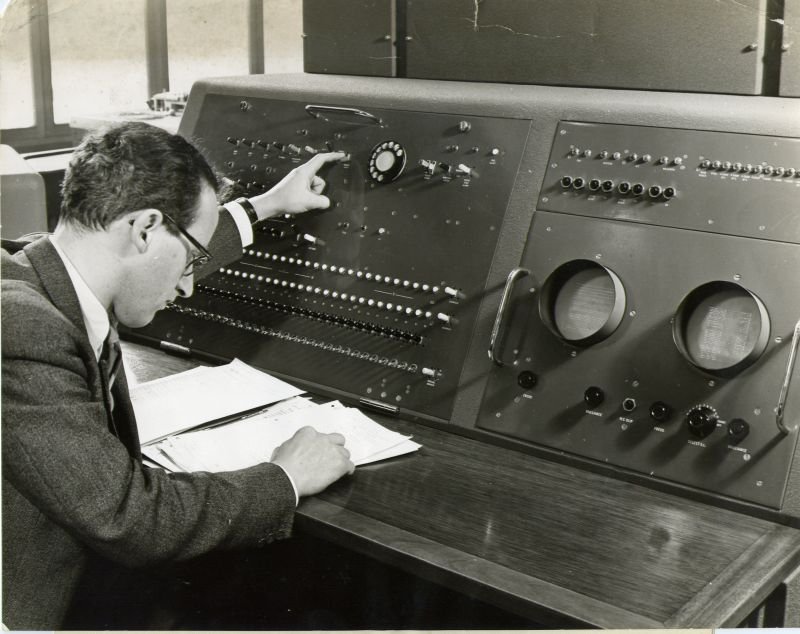
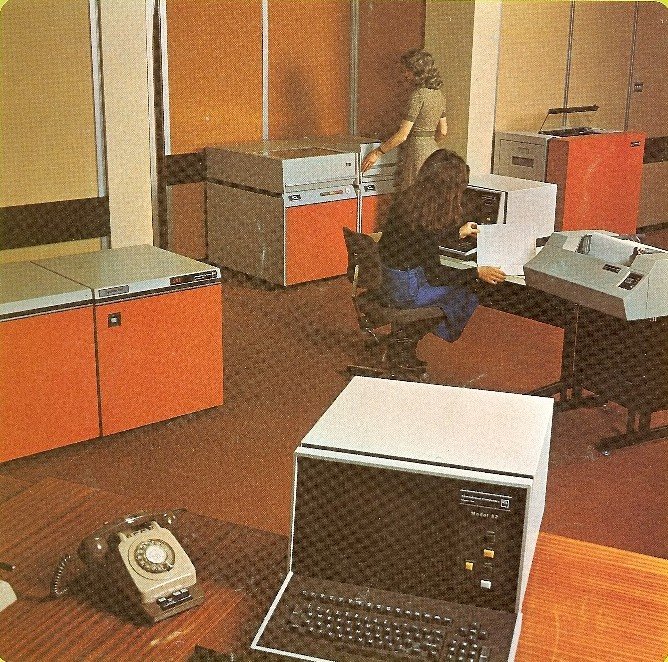
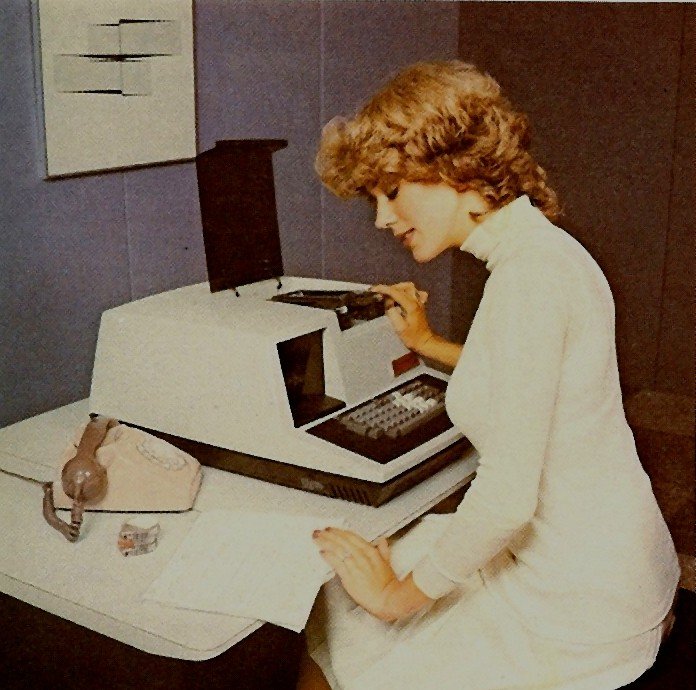
Readers will notice the appearance in this issue of six brochure photographs of computing machinery accompanied by attractive young ladies. It seems doubtful whether this practice ever helped sell a single machine. Nevertheless it still goes on today, nearly 50 years on. Why?
The Society has its own Web site, which is located at www.computerconservationsociety.org. It contains news items, details of forthcoming events, and also electronic copies of all past issues of Resurrection, in both HTML and PDF formats, which can be downloaded for printing. We also have an FTP site at ftp.cs.man.ac.uk/pub/CCS-Archive, where there is other material for downloading including simulators for historic machines. Please note that the latter URL is case-sensitive.
| Top | Previous | Next |
This year marks the 800th anniversary of the founding of Cambridge University. And on 6 May, it was exactly 60 years since EDSAC, the first stored program computer in the world to enter service, ran its first program. The achievement is marked by the University in its anniversary brochure, in which EDSAC’s creator, Professor Sir Maurice Wilkes, stands shoulder to shoulder with Isaac Newton, Charles Babbage and Sir Frank Whittle.
 |
|
Professor Sir Maurice Wilkes |
As you would expect, the date did not pass unnoticed. On the afternoon of the 6th, the great and the good of the University, movers and shakers, past and present, gathered together to celebrate. And what a celebration it was! Around 300 souls, including assorted members of the Computer Conservation Society, listened to Professor David Barron, formerly of Southampton University, giving the opening address which described the experience of using EDSAC 1 in the early 1950s and considered the hardware and software available to users. The late David Wheeler′s ″Initial Orders″ which comprised not only a means of loading programs for execution, but also a primitive assembler, came in for particular attention as did the creation of the concept of subroutines and a subroutine library - all world firsts.
Professor Barron was followed by Dr. Doron Swade, late of the Science Museum and the world authority on the work of Charles Babbage. Doron observed that EDSAC was the marker that made visible a new constituency of practitioner - the user. He continued by saying that EDSAC and Wilkes not only implemented the stored program concept in a usable machine, but, it could be argued, helped define two of the several features that make up what we mean by a stored program machine. There also appeared to be a lack of agreement amongst historians and computer pioneers as to what exactly was historically significant about the stored program development, and he posed the question “in what respect is a computer logically and historically different from any other machine?”
Finally, Sir Maurice thanked the speakers and acknowledged the enthusiastic acclamation of all those present.
A reception and a high table celebratory dinner followed. The entire event was orchestrated by CCS Chairman David Hartley with the style and panache to which we have been fortunate to become accustomed.
It is hoped to publish a full account of the lectures in due course.
-101010101-
Following the April CCS lecture at the Science Museum on the occasion of the 25th anniversary of JANET, a celebratory dinner was held for the leading members of the JANET community. Three of them were honoured.
Mike Wells was one of the initiators who visited the US in 1972 to examine the fledgling ARPANET and was inspired to recommend a UK equivalent. He became JANET’s first Director of Networking.
Roland Rosner was the first head of the Joint Network Team which preceded JANET and was responsible for the strategy which led to the creation of JANET in 1984.
Finally our own David Hartley was recognised having been a major supporter of JANET within the Computer Board at the outset and having become chief executive in 1994. David it was who had to explain to British Telecom (who still had a statutory monopoly on telecoms in 1984) why JANET needed to be independent of them. No reply was forthcoming which was taken as authority to proceed. It was said that David was far from unique in failing to obtain any response from BT, but that it was an unparalleled blessing for JANET!
-101010101-
The National Museum of Computing featured in the Observer’s list of obscure museums in their April supplement Secret Britain. Other mysterious museums mentioned included the Bakelite Museum and the Sandtoft Trolleybus Museum in darkest Lincolnshire.
More quiz news courtesy of Private Eye. The Weakest Link asked “Charles who is said to be regarded as the father of modern electronic computing?” “Darwin” was not accepted as the correct answer. But quite what answer was expected is not entirely clear either.
In June, “Charles Babbage” was the answer to a pub quiz question in an episode of Kingdom. The question, however, was not revealed.
Clearly our mission to convince the public that computer history is to be valued has some way to go. But we are, at least, on the agenda.
Late May saw the arrival of a suite of Powers-Samas punched card equipment at the National Museum of Computing. There are some 12 items, mainly 40-column equipment including slightly earlier versions of the equipment shown below. The equipment is not currently working but is thought to be restorable and, it is hoped, may be on display soon.
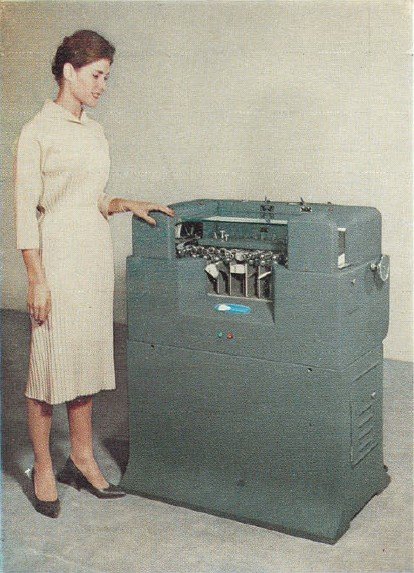 |
Collator |
 |
|
Interpreter |
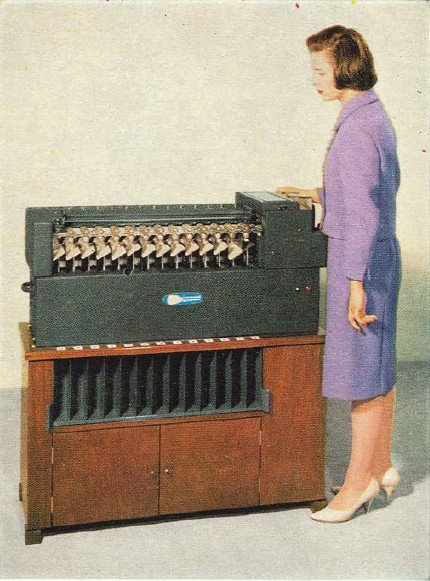 |
Card Sorter |
 |
|
Summary Card Punch and Tabulator |
-101010101-
In Resurrection 43 we reported that the Museum of Computing in Swindon had closed, having lost its premises. We are delighted to hear that new and better premises have been found and that the museum re-opened with due ceremony at the end of June with representatives of the Computer Conservation Society in attendance. Go to www.museumofcomputing.org.uk for details.
-101010101-
September 2010 is the date, Brisbane is the place, IFIP is the organiser and the World Computer Congress is the name. The 50th anniversary of IFIP will be celebrated with a series of conferences including a History of Computing conference. The content will be broad but includes the history of hardware, software, companies and people - meat and drink for the Computer Conservation Society. A call for papers at www.wcc2010.org is the starting point.
-101010101-
Strange goings-on at Bletchley Park are reported by Bombe team member Paul Kellar -
Not for the first time in this project, I think we have solved another long-standing mystery: Why did Alan Turing chain his coffee- cup to the radiator? The answer lies in what has happened to our coffee machine: it′s vanished!
Clearly there is a coffee-poltergeist of German origin in the Park, who has been fooled by our success and Turing′s statue into thinking that we, like him, needed to be stopped.
I have invested £6.00 in a replacement. I think we have earned the right to chain it to the radiator. We should regard it as a compliment that we have shown up on the poltergeist′s radar.
Contact detailsReaders wishing to contact the Editor may do so by email to |
| Top | Previous | Next |
ICT 1301 - Rod Brown
This is the first report since the CCS offered the 1301 project the opportunity to become a working group.
The Machine has now re-stabilised after the overwinter period. The current calculated status is 94% towards the first aim of the project, which is to start recovering application software. Recovery software is still under development and we can now connect a laptop PC to the machine via a software-driven UART (serial interface) to create a path to unload the code recovered from half inch magnetic tapes and packs of 80 column cards. We hope to have started to recover some initial software by the end of 2009.
The machine now has two additional drums connected. The priority now is to rework the covers to secure the new cabinets and make the new area visitor safe. After that we can start to investigate the functional status of the drums and plan the integration of them into our general usage and demonstrations.
The first of the many manuals we hold is now available for download, in PDF format. More manuals will follow as they are prepared, but in choosing the first manual it just had to be the 1301 Programmers Reference Manual. This item has been referred to by so many visitors to the website we hope it will be a popular item. Further manuals are in an advanced state of preparation and will be presented on the website www.ict1301.co.uk.
The first of the card file pack images will start to be available in the latter half of 2009 (once we recover from the annual open day event). At that point the full functional specification of the machine will be available online, however we do not see that either of the Emulators / Simulators will be available before late 2010 at the earliest.
Many thanks to all who visited and joined in on the day. Bruce McMillan who worked on 1301 in New Zealand was most happy with the day and we hope everyone found something of interest. The event is covered on the project website for all to view. Now that we are onboard at the CCS, the project would like to offer visits to any members who would like to understand what we are trying to do and perhaps might consider offering to help with the project. We will respond to any emails we receive from the website and are planning another open day in August/September of 2009 should there be sufficient interest
The Committee is attempting to produce a register of vintage films about the machines and systems that are of interest to our members. To that end we would like members to let us know if they personally have copies of such media - whether on film, video cassette, or DVD. The initial list is at www.computerconservationsociety.org/media.htm.
If you can help to add to this list, please email Kevin Murrell at kevin@ps8.co.ukwith as much detail as you have.
The Manchester “Baby” replica computer has now been in the Museum of Science and Industry in Manchester for over a decade. And almost every Tuesday for the last 10 years, it has been demonstrated in front of museum visitors by a team of enthusiasts many of whom were involved in the building of the replica. Time, however, marches on and the ranks of volunteers are wearing ever so slightly thin. In a way this is excellent news, for it provides an opportunity for anybody living within reasonable reach of Manchester to join the happy band. The team would love to hear from anybody who would like to join them. 1940s engineering skills are not required, though no doubt they would be welcome. What is needed is an ability to talk about the machine and its history to interested museum visitors - something which should be no problem to the average member of the Computer Conservation Society! Obviously detailed training is on offer and you would not be expected to face the public on your own.
So, if you’ve ever felt it would be fun to join this very special group of people, this is your chance. Contact Cat (Catherine Rushmore) by email at c.rushmore@mosi.org.uk or on 0161 606 0116.
Bombe Rebuild Project - John Harper
This is the second part of my report relating to the extra diagonal board that we made recently. This is now complete and fully tested. As mentioned in Resurrection 46, we have proved to our own satisfaction that the two extra features function as they did in WWII.
I will now describe the second feature, SSS (Self Stecker Selection)
A proportion of the later Bombes were fitted with an SSS jack on their Diagonal Boards. This facility was used in a menu when the cryptanalysts were confident that at least one of the letters of the menu was self-steckered i.e. not steckered to any other letter.
The 26 pins of the SSS jack were wired to the 26 self-stecker points (A/a, B/b etc) of the Diagonal Board. Normally these self-stecker points would have no connection and thus would never contribute in finding a stop.
When used, the SSS jack was cabled to a common (a group of four or five jacks connected together in parallel) using a standard menu cable. An EEL plug, a plug with 26 sockets into which up to 26 individual connections can be made, was also inserted into this common and a daisy chain cable plugged into the sockets of the EEL plug connecting together all the letters not on the menu plus the input test letter. Finally the common was connected to the chain input jack.
Since the chain input jack is wired to the test letter input switches, the input of the spider (the interconnected Letchworth Enigmas comprising the cabled up menu) and to the chain’s sense relays, the daisy chain in the EEL plug ensures that there is always voltage on the self-stecker points of the off-menu letters and hence that these cannot contribute to a stop. When the Bombe is running the sense relays only ever see the self-stecker points and thus, if it stops, the letters indicated must all be self-stecker points without voltage on them.
Supporters will be pleased to hear that we have received even further generous donations to complete our extra drums. However we still need to raise £800 to complete the 20 additional drums.
Our website is still at www.bombe.org.uk/
| Top | Previous | Next |
 |
|
Seymour Cray |
The first hint that Seymour Cray might have some aptitude for logic design came in 1935 when at the age of 10, he built, from Meccano, a machine to convert paper tape information to Morse code - no mean feat, even today.
In 1950, Cray joined Engineering Research Associates and worked on the development of the ERA 1101, the first US computer to be built for sale. ERA was soon acquired by Remington Rand along with the Eckert-Mauchly Computer Corporation, and the ERA 1101 became the Univac 1101.
By 1953, Cray was the principal designer of the Univac 1103. However, a decision to concentrate on commercial data processing rather than scientific computing was resented by some of the former staff of ERA who also hated “big company bureaucracy”. So, in 1957, the Control Data Corporation was founded. Cray joined CDC as chief designer. From the outset, CDC used transistors rather than valves and the first of over 50 CDC 1604s was delivered in early 1960. Derivative designs followed, including the diminutive CDC 160A which Cray is reputed to have designed in the space of a single weekend.
By-passing CDC’s 3000 Series, Cray started on the design of the 6600 which was to be the world’s fastest computer at its launch in 1964. He demanded that development was isolated from the company’s day-to-day activities which he found distracting. Authority was given to set up a small team in his home town of Chippewa Falls, Wisconsin. Nobody, not even chief executive, Bill Norris, was allowed access without an invitation from Cray.
The story is told of a customer who arrived, program listing in hand, and knocked at the front door to demand attention to a problem. The door was answered by Cray himself who, after a cursory inspection of the code, made a short, uncomplimentary and distinctly Anglo-Saxon remark about the customer’s program, then turned on his heels and closed the door, leaving the customer standing alone outside.
 |
|
CDC 6600 Installation |
The genius of the 6600 was its ability to carry out many instructions in parallel. Instructions were normally initiated in the order in which they had been written but execution took place in one of 10 autonomous units each dedicated to a particular group of function codes. Consequently many instructions could be under way at any one time. The circuitry provided interlocks ensuring that dependencies were respected and instructions could be deferred until conditions allowed their execution. This, together with the variability of execution time for different instructions, meant that instructions might be completed in an order that was only vaguely based on the sequence which the programmer had specified.
Another novel feature of the 6600 was the use of (usually) 10 small processors (actually re-engineered CDC 160As) to handle peripherals and run the operating system. These “peripheral processors” needed no complex floating point circuitry and had modest performance, but relieved the expensive central processing unit of tasks which would have wasted its sophisticated hardware capabilities. Ingeniously, there was only one peripheral processor, but 10 sets of registers addressed in turn.
News of the 6600’s launch didn’t go down well at IBM. Tom Watson jnr. sent a memo -
Last week, Control Data... announced the 6600 system. I understand that in the laboratory developing the system there were only 34 people including the janitor! Of these, 14 are engineers and 4 are programmers. Contrasting this modest effort with our vast development activities, I fail to understand why we have lost our industry leadership position by letting someone else offer the world′s most powerful computer.
Cray’s response -
It seems like Mr Watson has answered his own question.
In time, the 6600 was joined by other, compatible machines which included not only dual processors, but asymmetric dual processors.
In 1969 CDC launched the 7600 deposing the 6600 as the world’s fastest computer. Essentially a re-engineered version of the same thing, it was between four and 10 times faster, but not quite order code compatible. The increase in speed was achieved by circuit miniaturisation and by the adoption of instruction pipelining. Despite reliability problems, the 7600 sold in respectable quantities, often as a 6600 upgrade. The 7600 usually had no peripherals, being front-ended by a more a modest computer - most often a CDC 6000 Series machine.
Cray’s next machine the CDC 8600, never saw the light of day. After development difficulties with cooling, CDC cancelled the machine and Cray resigned, setting up Cray Research in 1972.
 |
| Cray-1 |
Four years later, the first Cray-1 computer was delivered deposing, in turn, the CDC 7600. Extending the principle of pipelining to vector processing bought vastly increased performance once again, but to a more limited range of applications. The Cray-1 and its successor machines captured much of the market for supercomputers but, by the end of the 1980s, that market was in decline; partly as a result of the arrival of smaller and cheaper hardware which could be used cooperatively in large numbers, but also because the end of the cold war simply curtailed the requirement for ever-growing calculating capabilities.
In 1989, once again, Cray moved on, this time to set up the Cray Computer Corporation. The astonishing, gallium arsenide-based Cray-4 was announced in 1994. The Cray-4 was designed with up to 64 highly pipelined vector processors running at 1 GHz and delivering a remarkable 32 Gigaflops. But by then, the world had moved on. The following year the company filed for bankruptcy and the Cray-4 project was abandoned without having attracted any orders.
Shortly after starting again with yet another new company, Seymour Cray tragically died following a traffic accident in 1996.
Today, the influence of the CDC 6600 is very much still with us and can be seen in many modern processors. Cray Research lives on as Cray Inc having been bought and sold by Silicon Graphics and, of course, ERA and Univac’s successor Unisys survives. But of CDC, there is now but little trace.
Seymour Cray may have been a touch “difficult”, certainly intolerant of time wasters, but there is little doubt that he was one of the great computer designers of the 20th century.
| Top | Previous | Next |
In 1976, Singer Corporation decided to dispose of its subsidiary, Singer Business Machines, Inc. There was much industry speculation about who would acquire it and universal surprise when it turned out to be - ICL. This article sheds some light on why, how, and the consequences for ICL.
Singer Business Machines (SBM) was originally formed to support Singer Corp.’s retail operations. It became an amalgam of acquisitions, including Friden and Cogar Corporation, and took on an international life of its own, presided over by George Cogar, father of Univac 1004, Singer 1500 and the XS3 character code which they shared. SBM also developed ranges of factory data collection and retail point-of-sale (POS) terminals, clustered on System Tens or 1500s, and challenged IBM and NCR for dominance of the POS market, with some awesome sales, involving many thousands of terminals each, to stores chains like Sears Roebuck and J.C. Penney. By 1976, however, the contractual reliability obligations with major retail customers in the USA had become very onerous, and Singer decided to resolve them by disposing of SBM.
ICL in 1976 was a mainframe manufacturer. Even the successful ICL 2903 was a re-engineered 1900, hastily introduced originally to help plug a revenue gap arising from the delayed launch of the 2900 Series. There was a view within the company, spearheaded by Ed Mack, Director of Product Development, that ICL could and should stick to mainframes. It did not need small systems in its business model, did not “understand” them, not least in marketing terms, and they had no legitimate role as adjuncts to mainframe business; “distributed processing” meant “distributing incompetence”, and was simply a “faddy trend”, it was widely reported.
Speculation was rife in the industry: who would pick up SBM? The betting was on some US giant. Nobody suggested ICL, so surprise was widespread, not least within the company, when agreement in principle was announced for its acquisition of SBM. What were its, or rather Chairman Tom Hudson’s and Managing Director Geoffrey Cross’, motives?
On arrival in 1972, Cross had set goals to double revenues, with at least 50% from outside UK, in five years. A key reason was to make ICL’s mainframe product development (and support) budgets more sustainable. Such growth was not likely to be achieved just “organically”, nor by yet more development costs of new products for new markets.
With SBM, ICL firstly took care not to inherit the crippling POS maintenance obligations; TRW took over the US customer base. Secondly, little money changed hands until certain revenue achievement targets were met; initially, about $3.75 million, and a similar amount for the Utica plant. But what were the perceived opportunities?
 |
|
ICL System 25 derived from the Singer System Ten |
SBM had a large, profitable, international customer base, with a viable presence in many countries; not least in the USA, which ICL had long and expensively dreamed of penetrating (for reasons forever mysterious to the author). There were, for example, about 900 System Ten installations worldwide. They seemed to be everywhere, from on- board Baltic ferries to Indian Immigration Services, from the Royal Mint to local timber merchants. The customers were, largely, content and committed,relying on applications, mostly written by third- parties, in a powerful macro-assembler, and thus incompatible with any other systems (although there was an RPG II compiler). The main (mutually incompatible) SBM product lines, System Ten and 1500, were mature and reliable. Their users were accustomed to paying recurrent maintenance and software licence charges which advancing technology and competition had rendered exorbitantly obsolete; here was a substantial, steady revenue stream of near-pure gold. In time, most might be lured on to “real” ICL product lines. There were also proven small systems marketing, sales and support teams available, if required. From a traditional ICL perspective, the sales staff often seemed akin to market traders.
 |
| Singer 1500 |
As for the SBM products, ICL had nothing similar, but were they worth adopting for ongoing active marketing? System Ten was a significant interactive small business system, with transaction- processing connectivity and price-performance not matched by 2903, for reasons envied but not well understood. It also had a big catalogue of line-of-business application programs. It could, and occasionally did, support as many as 20 interactive dumb screen terminals; it could, and often did, support well over 100 POS terminals. The 1500 was a single-user terminal-computer, a sort of small-screen proto-PC with files held on dinky proprietary tape cassettes, which could be clustered on a primitive form of local area network. Then, notwithstanding the embarrassments in the USA, there was the POS terminal range. ICL had tried unsuccessfully to enter this burgeoning market, using terminals sourced from Anker.
Doug Comish was appointed Director in charge of Singer integration. Speed was essential. Personnel rationalisation was initiated, internationally, Comish himself playing a leading role. It was by no means simply a cull of the vanquished by the victors. In cases of duplicated management positions, for example, it was often the SBM candidate who survived or prevailed. About 2,500 staff joined ICL.
Led by John Panter, SBM’s development and manufacturing facilities were examined, partly to assess the feasibility of transferring both to the UK. A Product Rationalisation Committee (PRC) was established, to recommend what products, if any, should continue actively to be marketed, developed and manufactured and with what implications. This would clearly affect personnel and manufacturing decisions. The Committee consisted of Jeremy Walker, from Product Development Group, as leader, Alan Wakefield from Marketing, Keith Crook then from Systems and Technical Support, Michael Knight then from Product Planning.
The PRC had a day’s initial briefing on the products from SBM staff at Stevenage. The four then flew to San Francisco, visiting SBM’s development facility at San Leandro, home of Friden, for two days. Next, via New York Kennedy and Oneida County airports, the latter a large field with a large hut, to Utica, in upper New York State, home of Cogar Corp. George Cogar himself commenced the two day visit with a visionary address. Returning to London, the PRC attempted to digest the deluge of unfamiliar information, technical and commercial, just acquired, and a report was written, with recommendations and caveats. Not everything seen was recommended; omissions included a forward-looking Utica minicomputer, VP-16.
In terms of functionality and market positioning, the four main SBM product lines complemented the existing ICL range of products without clashes. They were, in descending business value, System Ten (not System-10, a DEC machine), so-called because it used decimal arithmetic; 1500; POS terminal range and factory data collection terminal range. A general concern was that they were all then six to seven years old. Their marketing life could surely not be stretched beyond 1979-80, and then only with rapidly fading results. What then? There were other, more specific concerns. Perhaps the most worrying one affected System Ten. Originally developed by Friden as a POS controller, this was also a very cost-effective business transaction-processing system, with sensible file management software (DMFII), using exchangeable disc drives. The Executive program was hardwired; multi-programming was achieved basically by time-slicing between up to 20 application “partitions”. The problem was that the drive supplies were no longer available, and stocks were small. No drives, no systems, no sales. ICL’s familiar FEDS and EDS40s could meet the need, but that would require interface developments, quickly. Another example was the POS terminals, needing reliability work, and functionally unsuitable for some tempting market segments, such as supermarkets. In various parts of the company, people started thinking about numbers and possibilities - even including emulation of System Ten on 2903.
There would surely be the need for a business plan, known then in ICL as a Programme Authorisation, or PA, if these products were to be duly adopted. The Director thought not, although a brief Management Summary paper would likely be needed. A PA, even for a new peripheral, could take weeks to compile, garnering and reconciling inputs, including caveats and weasel words, from involved corporate groups, before sign-off by all the executive directors concerned. In this case, there were four distinct product lines new to ICL.
One Thursday afternoon the Director announced a Singer PA was after all required, ready for review by Cross and sign-off the following Monday evening, anticipating presentation to a Main Board meeting the next day. Worse still, Cross had recently decreed that no PA should in future exceed 10 pages, including the financial spreadsheet. (This was produced using PROSPER, an ICL 1900 “financial planning” application, licensed to customers for a mere £6,000 p.a.). PAs had typically extended to around 20, even 40 pages. This was still the era of secretaries and typewriters, not conducive to intense editing. Somehow, by Monday, 6pm, sections of the draft document had been seized from various typewriters and hastily copied and collated. Signatories and some lesser folk assembled in Putney’s boardroom. Around 6:30, Cross arrived, glanced at his copy, said: “This is more than 10 pages. I’m not reading it,” and left.
Comish broke the stunned silence, and performed a rapid miracle on the Cross copy with finely judged scissor-work and less adept sellotaping, before retrieving a grim-faced Managing Director, who began to dissect the draft, belatedly revealing some important principles in the process. Most importantly, “adoption of these products will not involve any additional capital or development expenditure in this company year.” But it would, it must!? As 10pm approached, he had dealt only with System Ten, and ordered that all product sections be re-written in similar vein. He then dictated the management summary, inviting anyone to interrupt, “at his peril”. None did. Finally, he examined the signature sheet: “At least this page looks OK...author...M. Knight - with help, we should add. You can all sign it now to save time tomorrow. I want the new document on my desk by 10 am. You can have till noon for the spreadsheets.” This was not that gracious. His prescriptions had in effect changed the PROSPER PA model; defining such models was a black art vouchsafed to very few, and input was on punched cards, obviously.
Directors searched for ’phone numbers of secretaries who might be induced to come in very early, while the “author” went home to rewrite the text, nervously and in best handwriting. The four PROSPER sheets were re-run on the old model, hand-corrected to provide the required results (not easy in a hurry), and then typed. PA 123 received Board approval the following afternoon. It was quickly noticed that there were some errors in the handmade spreadsheets; mis-transcriptions and unreconciled rows and columns. It seemed to not matter.
Quietly, effort and even money were diverted to the adoption of the SBM products. This process deserves a separate story. System Ten got its new disc drives. The Utica plant became primarily a development and production centre under Frank Connors, focussed on 1500 and the terminal products, and also the white hope of the economically distressed Mohawk Valley, until its closure in 1987. System Ten hardware and software development and support groups were established, converging, in 1977, at Bracknell under Don Neely - probably an innovation for ICL! Production of System Ten moved from Albuquerque to Letchworth 1/3 factory, re-engineered as System Ten 220.
The 1500 and POS terminals achieved reasonable sales success; factory data collection did not. System Ten gained a new lease of life, boosted by the launch late in 1979 of a cost-reduced, limited- configuration version, System Ten-120, by which time it was clear the successor product, misleadingly code-named System 29, would be late. The PA in 1976 had optimistically estimated a further 980 System Ten sales, tailing off in 1979-80. As usual, Marketing got it wrong. In 1980-81 alone, about 1300 were sold, overlapping a low- cost, low-key, but confidence-building launch of the backward- compatible System 25, and helped by a “fire-sale” price reduction, to clear the Ten’s inventory. This proved embarrassingly successful; the sales surge was hard to stop, and a number of contracts had to be re-negotiated onto S25. (A little later, IBM took the same approach with its System 34 and new System 36, principal rivals of the Ten and 25.) With average sale values around £20,000, this was a significant revenue contribution, at a dark time in ICL’s history.
Meanwhile, the SBM acquisition had already contributed substantially to the achievement of the aforementioned Cross goals. ICL was committed to small systems - and distributed processing, for good or ill.
Author’s note: Contributions from several participants in the SBM acquisition are gratefully acknowledged. Michael Knight was System Ten/25 product line marketing manager, 1979-84. He can be contacted at michaelknight242@tiscali.co.uk.
| Top | Previous | Next |
Doron Swade is provoked to muse upon the meaning and purpose of museum objects. He questions their relevance in the modern world, but reassuringly concludes that they still retain pride of place.
The central article of faith in museum life is a belief in the primacy of original objects. Traditional museums are part of an object-centred culture. Physical artefacts, their acquisition, meanings and care, dominate the professional psyche of museum curators. Original artefacts are sanctified and prized above object surrogates - replicas, graphic depictions, holograms - for reasons that are not always easy to articulate. There is a new arrival in this sanctum of belief and tradition - the virtual object. By this I mean an electronic representation of a thing whether real or imagined. The creation and manipulation of computer-based virtual objects are compellingly attractive to museum directors, exhibition designers and educationalists. Yet the implications for museums and for the material culture that underpins museum practice are far from clear. Virtual objects agitate our assumptions about the status of the original and prompt a re-examination of the “work” an original object does in museum culture.
Before we can address the issue of whether or not virtual objects challenge the primacy of original artefacts it would be helpful to articulate what it is about original artefacts that privileges them in museum culture. In the 1980s the United Kingdom underwent a cultural revolution. Under “entrepreneurial Conservatism” accountability became the touchstone of efficiency. The public sector, national museums included, was not immune. Curators were asked to justify themselves to newly appointed accountants and managers imported from the private sector. As a curator at the Science Museum, I was asked by a new Director of Finance why the Museum needed original artefacts. “Why” he asked, “could we not make do with replicas?” To this day I ponder how an outwardly pleasant man could ask such a seemingly hostile question. Let us take the question in good faith, however it was meant. How does a curator justify the cultural or historical utility of original artefacts to a sceptic?
To the Director of Finance I offer the case of Napoleon′s waistcoat button. A curator is shown six objects. Because of financial constraints he/she has to choose one and only one of the six. The objects on offer are a button worn by Napoleon on his waistcoat at his final battle, a battle that he lost. The provenance of the button is impeccable and authenticated. The curator is also offered another button made by Napoleon′s button maker but not worn by Napoleon at the final battle. The third and fourth objects are replicas: a contemporary replica of the button and a modern replica, both physically indistinguishable at first sight from the original. The fifth object is a fake - a button purporting to be one from Napoleon′s waistcoat but which is not. The final object is a hologram of the original button. The curator has but one choice. In choosing only one object I would hazard that the curator′s instinct is to choose the original button worn by Napoleon at his final battle. The question is why?
Let us extend this hypothetical scenario. An historian advances a new theory: that Napoleon was allergic to snuff; that he took snuff for the first time on the eve of his great battle; that his strategic judgement was impaired as a result. Now it does not make sense to examine anything but the original artefact for traces of snuff in an attempt to verify this thesis. It would be equally meaningless to examine the two replicas or the fake since the issue of snuff content was unforeseen at the time of replication. Replicas embody physical predicates seen to be meaningful at the time of replication and reflect the state of knowledge at the time. In the absence of a snuff thesis at the time of replication, any examination of anything other than the original artefact, however useful in other respects, would clearly be meaningless. Only the original artefact will suffice for this forensic purpose. From this we can posit that the historical utility of original artefacts is their availability for interrogation in the light of unforeseen enquiry. Here the object is seen to embody an inexhaustible aggregation of predicates the full meanings of which are perpetually incomplete and revealed, if at all, through partial inquiry. We can argue from this that acquiring and preserving the original artefact is the only course of action consistent with the open-endedness of human enquiry. It is not suggested that artefacts are the only evidentiary source. Napoleon’s conduct during his final battle could doubtless be illuminated by other means - contemporary records, contextual and circumstantial evidence, military history, moral parables of hubris, and so on. But what partly underpins the value of original artefacts, and their enduring mystique, is the abiding sense that understanding is never complete, that knowledge is never total, and that the original artefact embodies evidence the meanings of which may not be accessible by other means.
The allegory of Napoleon′s waistcoat button can be used to argue the forensic utility to history of original artefacts. It also suggests that the mythological appeal of original artefacts might be underpinned by a sense of epistemic incompleteness that prompts us to endlessly visit and revisit episodes in history to reframe their meanings. It is not being suggested that the forensic utility of objects in history is their only value. But framing the meaning of objects in this way is both a device to argue utility to a sceptic and also one that provides an heuristic tool to explore object surrogates.
In the button scenario the forensic value of physical artefacts is founded on the notion of an object as an embodiment of physical predicates. By way of extending the argument it is useful to examine the predicate structure of a virtual object defined earlier as an electronic representation of a thing, real or imagined. It is assumed for our immediate purposes that the manifestation or representation of the virtual object is an image on a screen. Screen-based images are made up of hundreds of thousands picture elements (pixels). The features of each pixel dot can be independently manipulated - specifically colour and intensity. We can arrange the pixels in relation to each other just about any way we wish and in so doing depict entities of arbitrary shape, elongated, compressed or distorted beyond and independently of physical limits. Moreover we can manipulate the dynamic behaviour of the elements, or aggregations of elements, according to logical rules that are independent of physical rules of the thing depicted. In the virtual world stones can fall upwards, light bends round corners and two objects can occupy the same space at the same time.
The fact that we can manipulate each element of the representation enables us to construct representations at the visual equivalent of the atomic level. In addition, unlike say a construction from Lego bricks, a pointillist painting, or a photo-mosaic, each of which inhabits the no-mans’-land between parts and wholes, the resolution of screen-based electronic images can be increased beyond any discernable discontinuity. In computer-generated virtual worlds we can create images of anything we like, real or imagined. We can manipulate appearance and behaviour according to rules of our own devising and the behaviours are not bound by the rules of the things represented.
With this in mind we can ask whether virtual objects, whatever their other merits and appeal, have consequences for the primacy of original artefacts. Do they pass the test of historical utility? Can we interrogate them for answers in meaningful ways? I propose to explore these questions using two examples. One is a computer simulation of a nineteenth-century calculating engine, a machine that the inventor and designer, Charles Babbage (1791-1871), never built. The other is a simulation of an electronic computer, the Ferranti Pegasus, built in 1959. Each of these examples involves an electronic representation of a thing, one real, one imagined.
 |
|
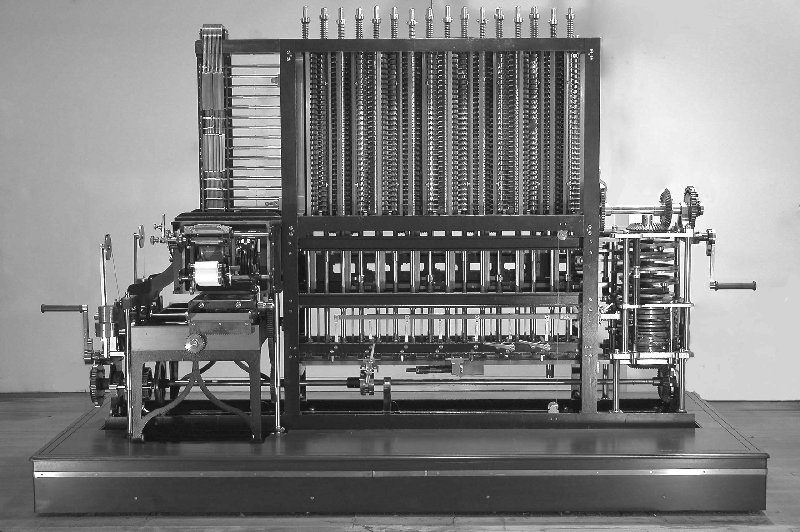
Difference Engine No.2 2005 |
The designs for Babbage’s Difference Engine No. 2 describe a vast mechanical calculating engine, 11 feet long, weighing some five tonnes and with 8,000 parts. The 20 drawings specifying the machine were completed by 1849, though no attempt was made in Babbage’s lifetime to construct it and the Engine remained unbuilt for over 150 years. Though the basic mechanism of the machine is comparatively simple, the design of the machine as a whole gives the impression of intricacy and complexity. As an explanatory aid to museum visitors a simulation was produced to explain the machine’s basic function. On screen, freed from the physical constraints of real mechanics, parts of the mechanism are suspended in space without the confusing clutter of physical support and without drive mechanisms which distract from the essential logic of operation.
For pedagogic purposes the computer animation builds up the mechanism on screen, part by part, through a process of progressive disclosure so as to craft the explanation in an incremental way; the operation of small parts is magnified by zooming; critical functions are repeated to highlight different aspects; perspectives are altered to offer new viewing standpoints and detail of otherwise hidden wonders; and the rhythm of real-time operation can be stretched, contracted and frozen according to the explanatory needs of the spoken commentary. The illustrative and explanatory power of such techniques is formidable. The power of these electronic representations does not only lie in the ability to depict motion. Stills - frozen frames - derived from the simulation enjoy the benefits of the visual essentialism such representation offers.
The representations of the Engine′s mechanisms on screen were not derived from the physical machine. Dimensions of parts taken from Babbage′s original drawings were input into a computer program to define the individual components and the programmer instructed the program how the parts were to move and interact according to an understanding of the principles and intended operation of the mechanisms. So the simulation, derived from the original drawings interpreted through understanding, exists quite independently of the physical machine. Clearly this simulation has educational and expository value undeliverable by the physical object. But does this virtual object undermine the primacy of the physical object as an evidentiary source? Can we interrogate it for answers in any meaningful way?
The freedom to represent the motion of parts independently of physical constraints derives from the separation of representation and thing. However, as we have seen, the grammar of electronic artefacts is unlike that of physical artefacts. Electronic representations are not bound by the physical laws of the objects or phenomena they depict. A human programmer instructed the computer to generate the images of the Engine and in the case of the Babbage simulation, the creation of the virtual simulation was found to carry its own unique hazards. In our ordinary experience it is impossible for two solid objects to occupy the same space at the same time. In the physical Engine the machine jams, fouls or breaks. The behaviour of electronic representations knows no such constraint. In the development of the simulation there were instances where meshed gears slide through each other as would ghostly phantoms. There were levers that moved without being activated by any causal connection with other levers, and there were instances of conditional behaviour that were simply wrong. These were errors of representation, not the result of any inherent restriction of the medium. Just as craftspersons making a physical replica use their skill to minimise physical difference between the representation and thing and mediates between the two, so the programmer mediates between the object (or the specification of the object) and the computer-generated image.
The example of the Babbage Engine simulation suggests that simulation as logical replication is no different in museological principle from that of physical replication in that such virtual representations incorporate intentional predicates bounded by the understanding of the maker - in this case, the programmer. Predicates perceived to be significant at the time of “replication” are consciously incorporated into the “object”, and these are a reduced set of predicates at that, that is to say, visual ones only. Such a simulation can be interrogated in much the same way as a physical replica. The example of the Engine simulation suggests that logical replication does not answer the challenge of historical utility and therefore has no significant implications for the primacy of the original in the sense discussed earlier, that is, in the sense of object as physical memory of contemporary conditions.
There is, however, a category of object for which logical replication embodies an inexhaustible set of predicates and where simulations can be interrogated in the light of unforeseen enquiry in ways that physical replicas cannot. The category of object is computers, and the example used here is that of the Ferranti Pegasus.
 |
|
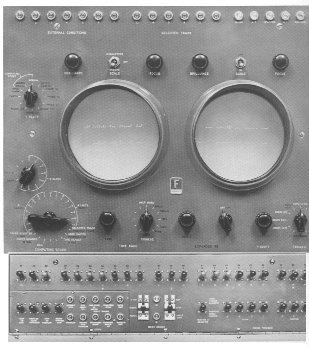
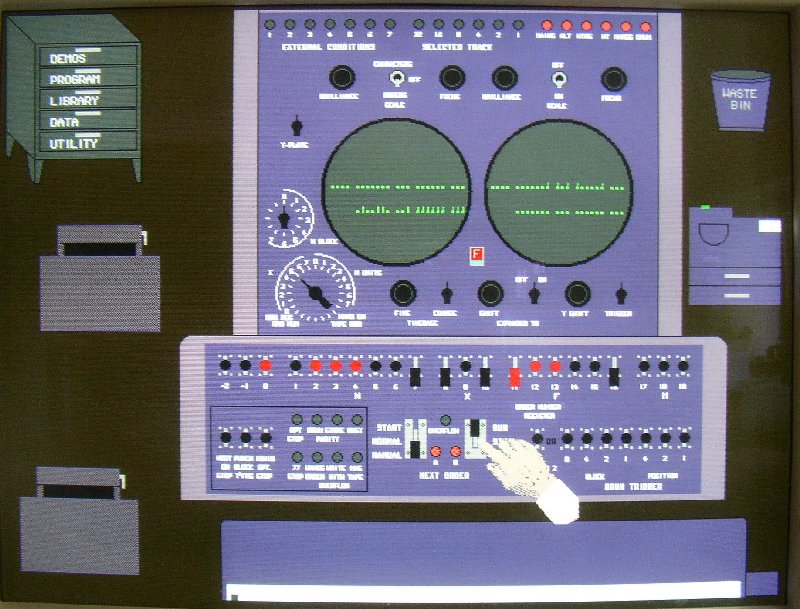
Pegasus Console |
The Science Museum’s Pegasus is a large electronic vacuum-tube computer built in 1959. It consumes 18KW of power. It was a respectable performer in its day though by present day standards it is better at central heating than calculation. The machine was restored to working order by a dedicated working party of the Computer Conservation Society. Pegasus is the only working contemporary vacuum tube computer I am aware of. It is a sad fact that however skilled the practitioners, and however conscientious they are in restoring and nurturing the machine, Pegasus will at some point become unmaintainable. When it comes to archaeological time scales, restoration to working order can do no more than defer the inevitable.
 |
|
Pegasus Simulator |
However, the Pegasus computer has been simulated (see Chris Burton’s excellent account at: www.computerconservationsociety.org/Pegasus%20Personified-1.pdf). The simulation is a bit-level simulation, that is to say, it is implemented at the logical equivalent of the molecular level of the machine. It replicates the behaviour of the operating system exactly and animates the on-screen console in response. The simulation captures the behavioural persona of the machine in all its detail including any bugs and quirks in the built-in operating system. The operator of the simulator, using a keyboard and mouse can, in the virtual world of the simulator, punch and read paper tape to program the machine, debug and run the programs, capture results and even monitor, as would an operator using the physical machine, the internal signals which appear as oscillograms on the console screen. The issue is not the fidelity of the simulation to the physical original in respect of shape, texture, colour, or the visual detail of the operating console, but the degree of completeness of the logical replication, which is exact.
The Pegasus simulation raises a number of issues. One such is the issue of artefactual identity. Because the world of museums is object-centred we assume through habit and convention that what we refer to when we talk about Pegasus is the physical machine. But it can be argued that computers, unlike steam locomotives or microscopes, have an identity that transcends their physical implementation. In his famous “cold porridge” speech Alan Turing (1912-1954), the English mathematician and computer pioneer, argued that what defined a computer was not the medium of its physical implementation but the logical rules by which it operated. In a speech to the pupils of Sherborne, his old school, he likened the appearance of the human brain to the cold porridge he recalls being served at breakfast as a school boy (“grey and soft and wrinkled on top”). Despite the resemblance of brains to porridge we do not hesitate to accept that brains think. Turing asserts that what is important is not the what we might now call “wetware” but the rules by which it operates and, by analogy, it is not the physical medium through which rules are realised that is significant, but the rules themselves. He argues that computers are universal machines that can be instructed to comply with any set of rules that can be described in symbols. One computer can therefore be fed the complete set of rules by which another computer operates. One could argue that the identity of the machine, defined by, and resident in its rules, has been transferred. It seems then that the identity of a computer is not exclusive to its physical hardware which may be regarded as accidental to existence but is at least partly, if not wholly, owned by the logical rules that define its operation. In the case of computers, identity is abstract and replicable without loss and without a reduction in the original predicate set.
If one computer is programmed at a sufficiently fundamental level to function in accordance with the rules of another, we have in fact an operational replica perfect in all logical respects to the original, including any imperfections in the operating system. We can run programs never run before. If we wish at some future time to know whether in the 1950s there was enough computing power to solve the trajectory equations of a missile fast enough to act as a guidance system, the Pegasus simulation can be used to find out. Logical replication of this kind captures the persona of the machine, and its behaviour can be interrogated in the light of unforeseen enquiry. In this respect we have a virtual object in the sense of being an electronic representation, as well as echoing the immateriality of the software that embodies its identity. And this particular class of virtual object does appear to answer the test of historical utility as evidentiary source.
One could argue that the computer running the simulation is itself subject to generational obsolescence and offers little to the custodial ambitions of museums to preserve machines in perpetuity. The simulation now runs on a Pentium-based platform but what will it run on in years to come? With the promise of machine-independent software there is the prospect of migrating the same simulation from one generational platform to the next and achieving, in the purity of logic, a kind of immortality - the dream of every conservator. So, in some respects, in the special case of electronic computers, logical simulation as a virtual object survives the forensic test of historical utility and suggests in prospect a salvation for the conservator for whom deterioration spells failure.
As an exploratory device I have narrowly defined the utility of original objects in terms of their historical utility as evidentiary source. In this respect I would say that virtual objects do not pose a threat to forensic history for the same reason that physical replicas do not, however attractive and instructive replicas might be to the museums and their public. If objects are viewed as physical memory of contemporary pasts, the virtual poses no material challenge to the real. In the special case of electronic computers, the virtual object - a simulation - challenges our ideas about artefactual identity as well teasing us with novel prospects for preservation. Separately from this, the real is under no threat from the virtual where virtual objects are used as expository aids, and in the appropriate context virtual objects offer unparalleled opportunities for new genres of representation and display.
1 This article is an edited version of earlier articles exploring similar ideas
Editor’s note: Doron Swade is the former Curator of Computing at the Science Museum in London. He can be contacted at doron.swade@blueyonder.co.uk.
| Top | Previous | Next |
Many of the leading figures involved in UK computing joined an overflowing congregation at Peter Hall’s memorial service in April - warm testimony both to his distinguished contribution to a vital industry and to his vibrant personality.
Hall worked at the leading edge of technology in a 39 year career. Graduating with a first class engineering degree, he was engaged in advanced projects at the Royal Radar Establishment throughout the war. Headhunted by Ferranti after a brief spell with the Atomic Energy Authority, he became manager of its computing department and then, after its acquisition by ICT, joined the planning and technical team as director of the group responsible for the design and manufacture of large processors.
In what, in some respects, was a golden age for UK owned computing, Hall was in his element. But he probably made his greatest contribution when he moved to ICL′s Worldwide Marketing Group with particular responsibility for UK government and related markets. This was the time of the single tender hardware procurement policy conceived to secure the bulk of government′s computer orders for ICL. Though well-intended, it was ineptly constructed, and could have been a disaster. That it worked effectively in practice was attributable to Hall and the scintillating team of young lions he assembled around him. He displayed to the full his qualities of judgement and common sense, reinforced by total integrity and honesty. He worked closely with senior Ministers and officials earning their trust and respect. It benefited ICL greatly.
In parallel with his work, and continuing long after formal retirement, Peter rendered great service to his profession. He served two terms as President of the British Computer Society at a crucial period in its advancement. He was a long-standing director of the National Computing Centre and contributed effectively to the governance of both Queen Mary′s London, and Manchester University. Well into his 80s he was a keynote speaker and dynamic participant in well attended seminars on computing developments.
Peter Hall was never one of the “life is deadly, life is earnest” school. His whole being was illumined by his enthusiasm and ebullient sense of fun. Together with his cultivated interest in and patronage of the arts and music this made for a memorable colleague and companion.
| Top | Previous | Next |
| 17 Sep 2009 | History of Comms | David Parsons |
| 15 Oct 2009 | ICT 1300 | Rod Brown |
| 17 Dec 2009 | Pegasus @ 50 | Panel of Speakers |
| 14 Jan 2010 | 50 years of Advanced Programming | Panel of Speakers |
| 18 Feb 2010 | The CDC 6600 | Dik Leatherdale & John Fernbank |
| 18 Mar 2010 | WITCH & CADET | Kevin Murrell |
| 15 Apr 2010 | Film Afternoon | |
| 20 May 2010 | Research Machines | John Leighfield |
London meetings take place in the Director’s Suite of the Science Museum, starting at 14:30. The Director’s Suite entrance is in Exhibition Road, next to the exit from the tunnel from South Kensington Station, on the left as you come up the steps. Queries about London meetings should be addressed to Roger Johnson at r.johnson@bcs.org.uk, or by post to Roger at Birkbeck College, Malet Street, London WC1E 7HX.
| 15 Sep 2009 | Iconic Machines : Exhibiting a History of Computing | Doron Swade |
| 20 Oct 2009 | The Evolution of Hard Discs | Neil Macphail |
North West Group meetings take place in the Conference Room at the Manchester Museum of Science and Industry, usually starting at 17:30; tea is served from 17:00. Queries about Manchester meetings should go to William Gunn at william.gunn@ntlworld.com.
Details are subject to change. Members wishing to attend any meeting are advised to check the events page on the Society website at www.computerconservationsociety.org for final details which will be published in advance of each event. Details will also be published on the BCS website (in the BCS events calendar) and in the Events Diary columns of Computing and Computer Weekly.
MOSI : most Tuesdays at 12:00 and 14:00. Demonstrations of the replica Small-Scale Experimental Machine at the Museum of Science and Industry in Manchester.
Bletchley Park : daily. Guided tours and exhibitions, price £10.00, or £8.00 for concessions (children under 12, free). Exhibition of wartime code-breaking equipment and procedures, including the replica Bombe and replica Colossus, plus tours of the wartime buildings. Go to www.bletchleypark.org.uk to check details of times and special events.
The National Museum of Computing : Thursday and Saturdays from 13:00. Entry to the Museum is included in the admission price for Bletchley Park. The Museum covers the development of computing from the wartime Colossus computer to the present day and from ICL mainframes to hand-held computers. See www.tnmoc.org for more details.
Science Museum : alternate Wednesdays 11:00 to 15:00. Pegasus “in steam” day. The first date in 2009 was 14 January.
North West Group contact detailsChairman Tom Hinchliffe: Tel: 01663 765040. |
| Top | Previous | Next |
[The printed version carries contact details of committee members]
Chairman Dr David Hartley FBCS CEng
Vice-Chairman Tony Sale Hon FBCS
Secretary, Chairman DEC Working Party Kevin Murrell
Treasurer Dan Hayton
Science Museum representative Dr Tilly Blyth
TNA representative David Glover
Bletchley Park volunteers representative Pete Chilvers
Chairman, Elliott 803 Working Party John Sinclair
Chairman, Elliott 401 Working Party Chris Burton CEng FIEE FBCS
Chairman, Pegasus Working Party Len Hewitt MBCS
Chairman, Bombe Rebuild Project John Harper Hon FBCS CEng MIEE
Chairman, Software Conservation Working Party Dr Dave Holdsworth CEng Hon FBCS
Chairman, ICT 1301 Working Party Rod Brown
Digital Archivist & Chairman, Our Computer Heritage Working Party
Professor Simon Lavington FBCS FIEE CEng
Editor, Resurrection Dik Leatherdale MBCS
Web Site Editor Alan Thomson
Archivist Hamish Carmichael FBCS
Meetings Secretary Dr Roger Johnson FBCS
Chairman, North West Group Tom Hinchliffe
Dr David Anderson
Professor Martin Campbell-Kelly
Peter Holland
Dr Doron Swade CEng FBCS MBE
Readers who have general queries to put to the Society should address them to the Secretary: contact details are given elsewhere. Members who move house should notify Kevin Murrell of their new address to ensure that they continue to receive copies of Resurrection. Those who are also members of the BCS should note that the CCS membership is different from the BCS list and is therefore maintained separately.
| Top | Previous |
The Computer Conservation Society (CCS) is a co-operative venture between the British Computer Society, the Science Museum of London and the Museum of Science and Industry in Manchester.
The CCS was constituted in September 1989 as a Specialist Group of the British Computer Society (BCS). It thus is covered by the Royal Charter and charitable status of the BCS.
The aims of the CCS are to
Membership is open to anyone interested in computer conservation and the history of computing.
The CCS is funded and supported by voluntary subscriptions from members, a grant from the BCS, fees from corporate membership, donations, and by the free use of Science Museum facilities. Some charges may be made for publications and attendance at seminars and conferences.
There are a number of active Working Parties on specific computer restorations and early computer technologies and software. Younger people are especially encouraged to take part in order to achieve skills transfer.
| ||||||||||